An Intelligent Approach to Breach Resilience
Response, Resilience and Recovery
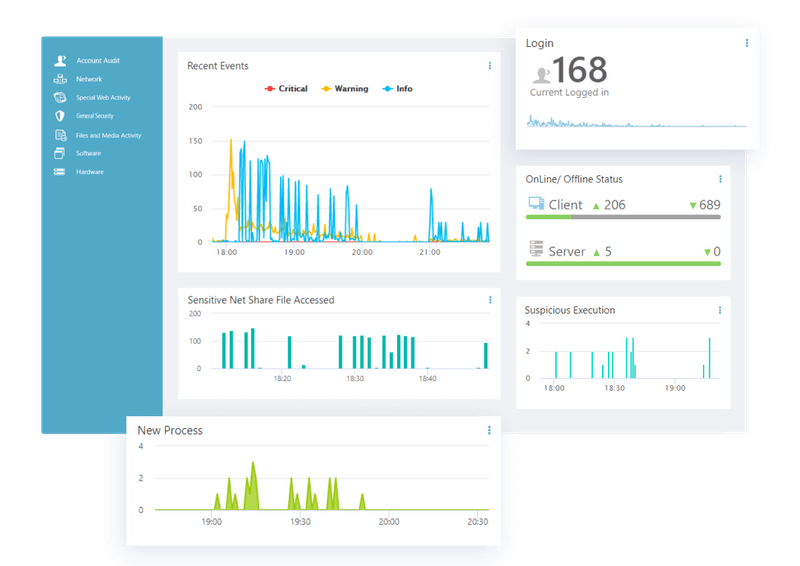
OREV is a self-contained cyber preparedness platform capturing data and change based telemetry in a very efficient manner.
Restores Normal Operations Post Breach
Think of OREV as a virtual “Digital Black Box” capturing 100% of all relevant data, providing first responders the tool sets to promptly identify the root cause and rapidly restore the network to a steady state.
Significantly reduces the amount of time of Breach Identification with Root Cause Analysis (RCA) and Triage completed in about an hour.
Eliminates the need for multiple tools and manual processes, mitigating business disruption and network downtime.
OREV Breach Resilience
Rapidly Restoring Normal Operations Post Breach

Intelligent Surveillance Technology (IST) Agents
Hardware and Asset Management
Out-of-the-box hardware management and visibility into network components, performance events and infrastructure failures. Monitoring and analysis is predictive as to potential failures and interruption of business activities, keeping the network viable 24/7/365.
Insider Threat Protection
Predictive insider threat monitoring and customizable behavioral detection through identity profiling, collating common attributes and continuous monitoring of all transactions to identify potential fraud.
Forensic Investigation
The “Orev Data Universe” The massive data collected and recorded by the Intelligent Surveillance Technology (IST) agents becomes a virtual “data universe”, a microcosm of all that transpired in the network, providing an actual subset, replicating the entire activity. The information aggregated facilitates the ability to recreate the tracing of the origins and causes of all events
Core Features
Attack Chain Visualization
Agent or Agent-less monitoring of every device on the network, in realtime. First detection, logins, software versioning, system access and more.
Efficiency
Visibility
OREV’s IST Agents work in realtime to perform twice-per-second analysis of activity. Instant analysis of all endpoints leads to more accurate threat and risk identification.
Risk Management
Monitor
Live Response & Remediation
Audit Trails
Do More with Less
The OREV Value Proposition
DETECT, RESPOND, RESTORE and REPORT
or application and restore the network…..all in real time.
- One centralized point of control for monitoring of all network operations
- Real-time dashboard visiblity reaching all endpoints and network components
- Maximum cybersecurity protection with instant notifications and actionable responses.
- Regulatory compliance and corporate frameworks, monitored and enforced online and offline.
- Scalable software that will work with hundreds and thousands of endpoints.
- Programmable real-time and historical reporting of all network operations.
- Realtime asset management and optimization, reducing operational costs.
- OREV is a low maintenance software system that significantly refocuses and reduces workload of the security and network maintenance team.
- No measurable interruption or slowdown of network operations
- Sunset multiple redundant software solutions and consolidate.
- Audit trail of all network applications processes and activities.
